mirror of
https://github.com/domainaware/parsedmarc.git
synced 2026-06-09 12:19:42 +00:00
15f7d269d5ae69dbf4664b57f20315fcfe2b0578
* Add ASN-domain aliases to base_reverse_dns_map.csv Adds 457 entries keyed on the `as_domain` values that ship in `ipinfo_lite.mmdb`, so that the existing reverse_dns_map can serve as a lookup table for IPs that resolve no PTR — the common case for many large senders. Before this change only ~33.8% of routed IPv4 space had an `as_domain` that matched a map key; after, ~84.0%. All additions are brands that were already represented in the map under a different rDNS-base key (e.g. `comcast.com` alongside the existing `comcast.net`), plus a handful of well-known operators that previously had no representation at all. Also promotes 10 entries out of known_unknown_base_reverse_dns.txt (a1.net, actcorp.in, ais.co.th, emirates.net.ae, eolo.it, fpt.vn, ibm.com, movilnet.com.ve, ote.gr, singnet.com.sg) — each is a well-known operator whose identity is unambiguous from ASN context even if the original rDNS base alone was inconclusive. No code changes; this is purely data, in preparation for a follow-up that wires `as_domain` into the source-attribution fallback path when a report row has no reverse DNS. Co-Authored-By: Claude Opus 4.7 (1M context) <noreply@anthropic.com> * Reclassify Zscaler as SaaS Zscaler is consumed as a self-service security platform, not delivered as a managed service, so SaaS fits better than MSSP. Co-Authored-By: Claude Opus 4.7 (1M context) <noreply@anthropic.com> --------- Co-authored-by: Sean Whalen <seanthegeek@users.noreply.github.com> Co-authored-by: Claude Opus 4.7 (1M context) <noreply@anthropic.com>
parsedmarc
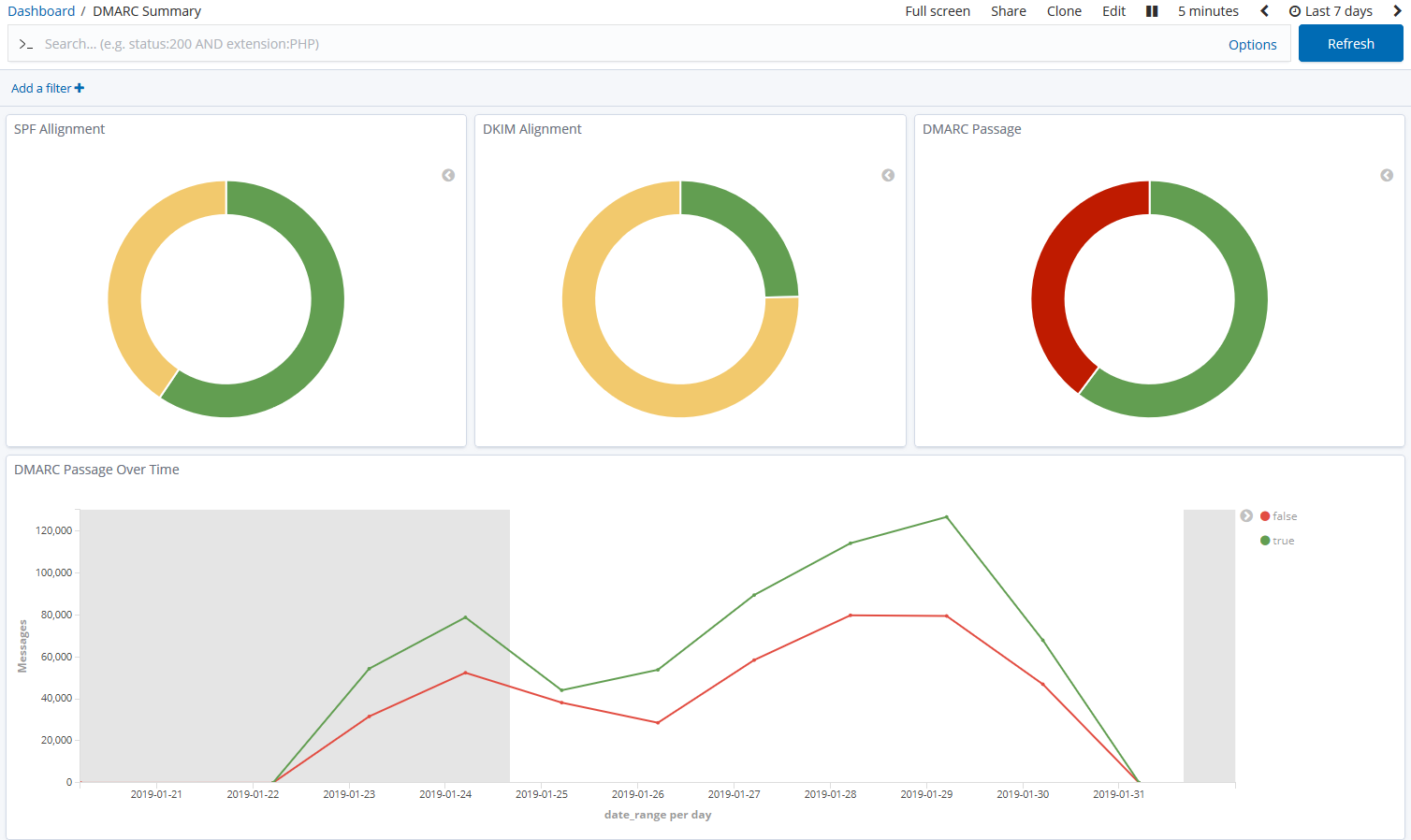
parsedmarc is a Python module and CLI utility for parsing DMARC
reports. When used with Elasticsearch and Kibana (or Splunk), it works
as a self-hosted open-source alternative to commercial DMARC report
processing services such as Agari Brand Protection, Dmarcian, OnDMARC,
ProofPoint Email Fraud Defense, and Valimail.
Note
Domain-based Message Authentication, Reporting, and Conformance (DMARC) is an email authentication protocol.
Sponsors
This is a project is maintained by one developer. Please consider sponsoring my work if you or your organization benefit from it.
Features
- Parses draft and 1.0 standard aggregate/rua DMARC reports
- Parses forensic/failure/ruf DMARC reports
- Parses reports from SMTP TLS Reporting
- Can parse reports from an inbox over IMAP, Microsoft Graph, or Gmail API
- Transparently handles gzip or zip compressed reports
- Consistent data structures
- Simple JSON and/or CSV output
- Optionally email the results
- Optionally send the results to Elasticsearch, Opensearch, and/or Splunk, for use with premade dashboards
- Optionally send reports to Apache Kafka
Python Compatibility
This project supports the following Python versions, which are either actively maintained or are the default versions for RHEL or Debian.
| Version | Supported | Reason |
|---|---|---|
| < 3.6 | ❌ | End of Life (EOL) |
| 3.6 | ❌ | Used in RHEL 8, but not supported by project dependencies |
| 3.7 | ❌ | End of Life (EOL) |
| 3.8 | ❌ | End of Life (EOL) |
| 3.9 | ❌ | Used in Debian 11 and RHEL 9, but not supported by project dependencies |
| 3.10 | ✅ | Actively maintained |
| 3.11 | ✅ | Actively maintained; supported until June 2028 (Debian 12) |
| 3.12 | ✅ | Actively maintained; supported until May 2035 (RHEL 10) |
| 3.13 | ✅ | Actively maintained; supported until June 2030 (Debian 13) |
| 3.14 | ✅ | Supported (requires imapclient>=3.1.0) |
Description
Languages
Python
98.3%
Shell
1.6%